[wiki] trails contribution
Subj. All related materials go here.
It is not available how to collaborate with trails in the wiki right? Thanks
Hello! Currently no. :( Take a little bit of patience. Not much time to sit-and-do this wiki-chapter...

Hi Mikhail,
I have organized much better and updated every hour and every 24 hours many more lists of the sources of my honeynet that I have distributed worldwide, can these sources be integrated into the Maltrail part? Here are the sources:
https://github.com/conexioninversa/MalwareIntel
Thanks
Hi MikeHail,
I have organized much better and updated every hour and every 24 hours many more lists of the sources of my honeynet that I have distributed worldwide, can these sources be integrated into the Maltrail part? Here are the sources:
https://github.com/reverseconnection/MalwareIntel
Thanks
By the way I am integrating the honeypots with Maltrail :-)
@conexioninversa what's the confidences level of C2_XXX lists at https://github.com/conexioninversa/MalwareIntel ?
i mean, this all looks like a fresh set of lists, while it would be pity to push FPs to regular users
Hi Miroslav,
I think they are very reliable. However, I must say that I have found a Cobalt Strike-type product in a government agency and that is why I have included the supplier and certificate, that can help the analyst.
I also look for JARM traces, certificates and different characteristics of the reversing of the attacks received. However, I usually look for and analyze the beacon, which is the best characteristic that indicates the possible adversary.
I also have to say that the list of IPs that I have in MalwareIntel is a clean and tidy process of some raw files that have, among other things, URi, URL, country, jarm, certificates and many other things :-)
However, you have just given me an idea and I am going to put the raw data in case it can help someone by seeing more information from those files.
I send you a link file here so you can see the content and then once analyzed and processed I convert them to txt or csv with only the IPs to make it easier.
(https://raw.githubusercontent.com/conexioninversa/MalwareIntel/main/C2_CobaltStrikeBeacon.json)
With these files I have created pulses in OTX for AlientVault and the truth seems that they are very successful. I have also sent these files to Anomaly framework and to the bank where I currently work, with very good results.
In any case, I understand your position since it is a private investigation and it can generate doubts.
Anyway thank you very much.
@conexioninversa you removed it? why? :D
@conexioninversa if you would leave it updated and if you say that it is reliable, i could easily do a new "feed" out of it (in whatever form it would stay)
wiki-article is not ready. reopen.
@conexioninversa you removed it? why? :D
Hi Miroslav, I don't understand, all the files are in: https://github.com/conexioninversa/MalwareIntel
@conexioninversa if you would leave it updated and if you say that it is reliable, i could easily do a new "feed" out of it (in whatever form it would stay)
Yes. My idea is to leave it updated as it says on the project page. It is wonderful to be able to collaborate with you.
@conexioninversa you removed it? why? :D
Hi Miroslav, I don't understand, all the files are in: https://github.com/conexioninversa/MalwareIntel
Hello! I can confirm, that yesterday was 404 for these links.
@conexioninversa if possible, you could contain all those findings inside one file (e.g. C2_All.csv), where you would put a new column with the name of each entry (e.g. metasploit). that way we would reduce the number of "feeds" (i.e. requests) required to fetch all the entries
@conexioninversa if possible, you could contain all those findings inside one file (e.g.
C2_All.csv), where you would put a new column with the name of each entry (e.g.metasploit). that way we would reduce the number of "feeds" (i.e. requests) required to fetch all the entries
Hi, I already have the file created and automated as C2_All.csv. Can you see if it's worth it?. Thanks https://github.com/conexioninversa/MalwareIntel/blob/main/C2_All.csv
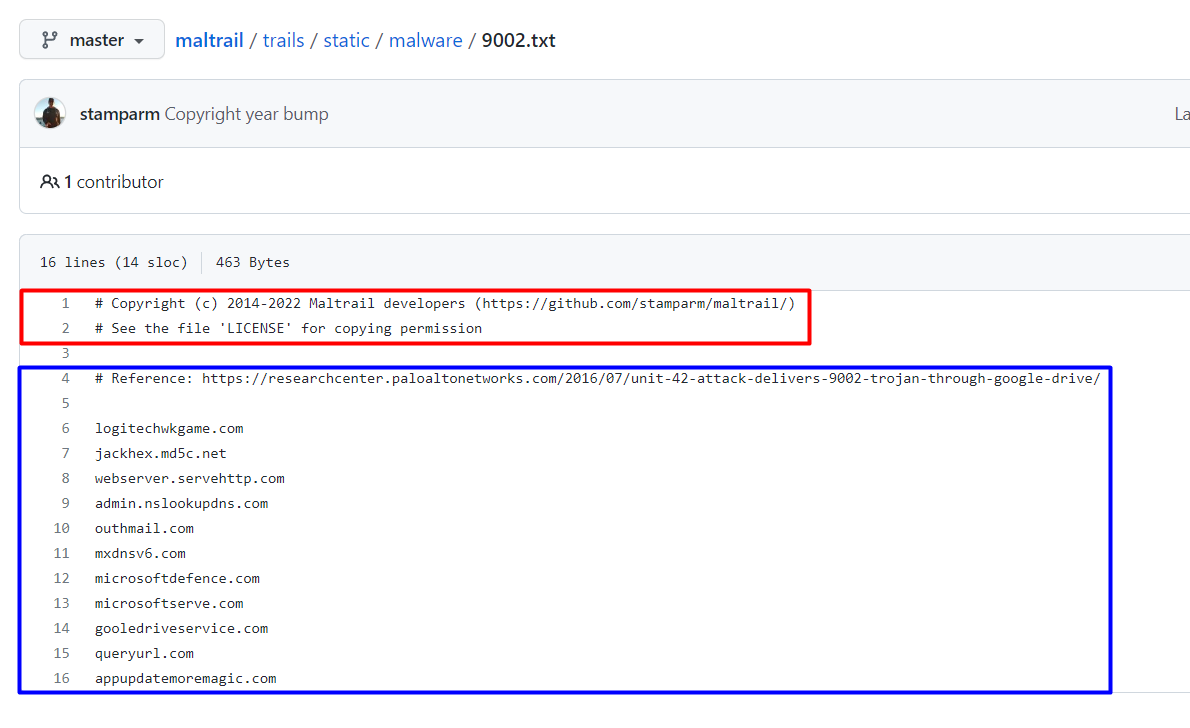
Currently goes as the updates for respective static trails:
[1] https://github.com/stamparm/maltrail/commit/9a155bfa41e24be62a839ea3de613ae134322354 [2] https://github.com/stamparm/maltrail/commit/99c9eea173614718d2d28edff99b4380d4c17939 [3] https://github.com/stamparm/maltrail/commit/c751ee1e8eb49f406608b3eaf9bf404a5330122f [4] https://github.com/stamparm/maltrail/commit/5a381ffe78786a0bff579632a921544eeac9269c [5] https://github.com/stamparm/maltrail/commit/a428a1bc979df2811588e5bde99d232f920ff709
Actualmente va como las actualizaciones para los respectivos senderos estáticos:
Perfect! Thanks

It is not available how to collaborate with trails in the wiki right? Thanks
Hello!
@conexioninversa Please, meet new wiki-articles, related to your question and to each other:
Maltrail trails structure - Information about Maltrail trails structure Maltrail trails base format - Information about Maltrail trails base format Maltrail trails contribution - Information about Maltrail trails contribution
Hope, you'll find useful and interesting information in them. If something is unclear in texts or some question(s) get be uncovered in articles, please, let me know -- will update the descriptions.
Thank you!
It is not available how to collaborate with trails in the wiki right? Thanks
Hello!
@conexioninversa Please, meet new wiki-articles, related to your question and to each other:
Maltrail trails structure - Information about Maltrail trails structure Maltrail trails base format - Information about Maltrail trails base format Maltrail trails contribution - Information about Maltrail trails contribution
Hope, you'll find useful and interesting information in them. If something is unclear in texts or some question(s) get be uncovered in articles, please, let me know -- will update the descriptions.
Thank you!
Perfect. Next week I'll get to it in order to have a base of collaboration according to the indications of the wiki. Good work
@conexioninversa Please, meet auxiliary tool, designed for trails contributing: https://github.com/MikhailKasimov/maltrail-dups-cleaner .
It would help to avoid adding trails (IP:port/domains/other type of trails), if they are already contained in static Maltrail bases. If any aspect of its usage would be unclear, please, let me know. Thank you!
Hi Mikhail Perfect. I have read the document. I understand that once the filtered file for duplications and registrations in the white list has been obtained, a pull request must be made, ok?
Hi Mikhail Perfect. I have read the document. I understand that once the filtered file for duplications and registrations in the white list has been obtained, a pull request must be made, ok?
... can be made. Generally this tool is optional: just to have a list for pull request for respective trail, which guaranteedly contains records are currently absent in Maltrail' static bases.
Can be closed because all related article are done:
Maltrail trails structure - Information about Maltrail trails structure Maltrail trails base format - Information about Maltrail trails base format Maltrail trails contribution - Information about Maltrail trails contribution