XSStrike
 XSStrike copied to clipboard
XSStrike copied to clipboard
Most advanced XSS scanner.
Thanks for this great project! I haven't tried it myself yet but it seems like a well-documented and mature tool to start using -- and it's under a year old!...
Hi , i am using a mac , and i scan an website for 2 hours and it is stuck at this step : Checking for DOM vulnerabilities WAF Status:...
I don’t know the plan without this feature in the later stage, because it is also important to find various vulnerabilities after logging in to the page.
In logs is row: core.requester - DEBUG - Requester url: http://blablabla.com Bee great if before this row was log row with url where this requester url was found. That will...
**Is your feature request related to a problem? Please describe.** A clear and concise description of what the problem is. Ex. I'm always frustrated when [...] **Describe the solution you'd...
**Describe the bug** Getting an error while running the tool. XSStrike manish$ python3 xsstrike.py -u "http://192.168.1.9/hidden.php" --data "my_token=d02ac44ef112819f0941ce0f077770b0&xss=test" --proxy XSStrike v3.1.4 Traceback (most recent call last): File "/usr/local/lib/python3.7/site-packages/urllib3/connection.py", line 171,...
**Describe the bug** When I execute the following,I'm going to get an error ``` (XSStrike) liuf2@liuf2-virtual-machine /u/l/e/XSStrike> python xsstrike.py -u "http://xxxx.xss.xx/level13.php?keyword=gs" -f "default" -d 5 XSStrike v3.1.2 Traceback (most recent...
**Describe the bug** Hi , Guys Executing xsstrike to add headers under Win 10 will result in an error, but execution under OS will be normal ?Please ... **Screenshots** 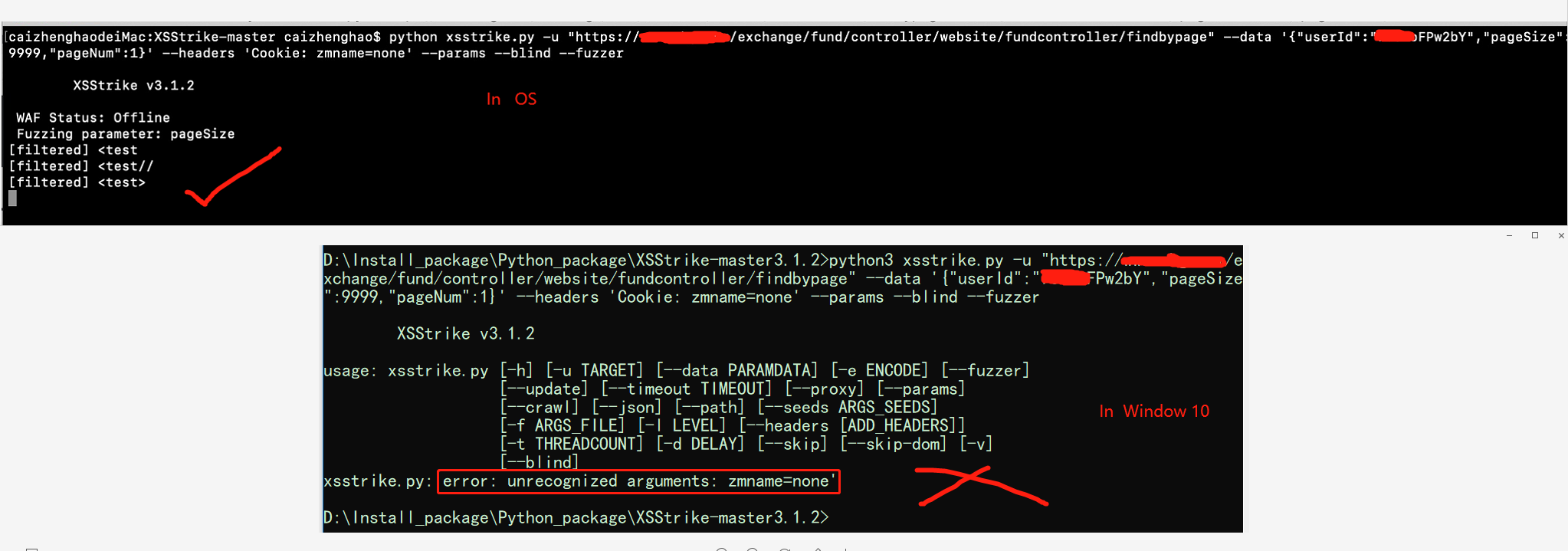...
**Is your feature request related to a problem? Please describe.** Suppose in the middle of execution, the program is forcefully quit, the user has to start from the beginning and...
Hi there! I have request with multipart form post request, how i can put it in xsstrike? `POST /vulnpage/ HTTP/1.1 Host: vulnsite.com User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:64.0)...
