Jean-François Roche
Jean-François Roche
> See also https://github.com/Mic92/dotfiles/blob/05daca459d96557eeeb72196258e6bffc73c1360/nixos/eve/modules/drone/exec-runner.nix for further hardening. The service is running with `ProtectSystem = "strict";` so everything should be read only. But I guess we better follow the principle of...
> See also https://www.ctrl.blog/entry/systemd-application-firewall.html Right we should have options to filter out internal/local networks
> Helsinki systems also had some useful apparmor presets that can be added on top. They archived their [bbb4nix](https://github.com/helsinki-systems/bbb4nix) repository. @Mic92 do you have more precise link in mind ?
rebased on master branch
Are we speaking about using /tmp during unittest not being secure ?
Yes the app diff contains the two extraneous secrets. Here is the application diff:  Here is the diff of one of the extraneous secret: 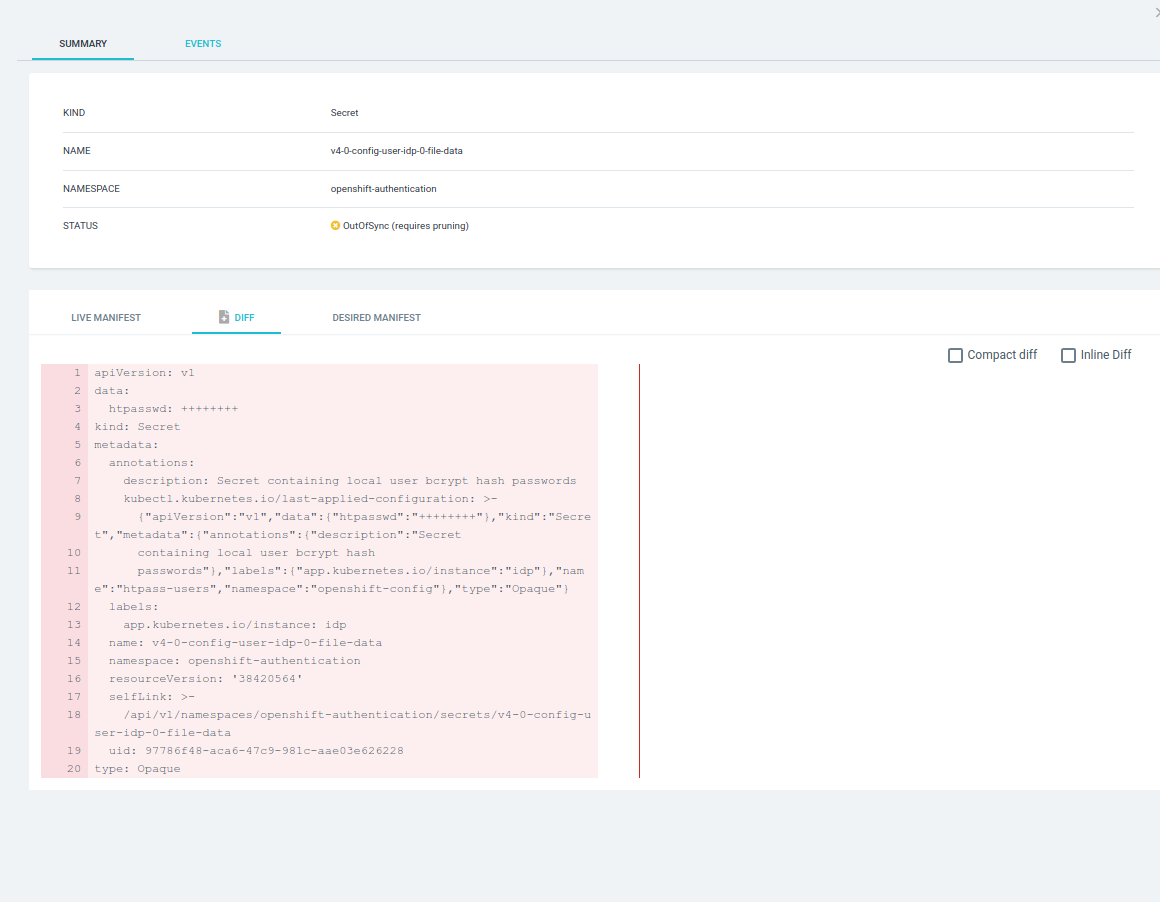
The extra resources are created by the operator so we have no control on their content (they are recreated by openshift if we try to remove them). Is there a...
@roberth I realize I may not have been clear earlier. Three days after your comment, I've pushed an implementation that should align with the new approach based on libgit2. I'm...
> What is the difference between this flag and using `path`-type explicitely? New users are most of time unaware of the distinctions between running it within or outside a Git...
> > This implementation also overlooks files that are specified in the .gitignore. > > Given the various ignoremechanisms in git (global [`XDG_CONFIG_HOME/git/ignore`], shared/in repo [`REPO_ROOT/.gitignore`], local [`GITDIR/info/exclude`]) we have...