Unrecoginized command received over pipe
This is my first try of AFL, but I'm unable to have it running properly, here is the source of the program I'm fuzzing:
/*
Author: Hardik Shah
Email: [email protected]
Web: http://hardik05.wordpress.com
*/
//a vulnerable c program to explain common vulnerability types
//fuzz with AFL
#include<stdio.h>
#include<stdlib.h>
#include<string.h>
#include<Windows.h>
struct Image
{
char header[4];
int width;
int height;
char data[10];
};
void stack_operation() {
char buff[0x1000];
while (1) {
stack_operation();
}
}
_declspec(noinline) int ProcessImage(char* filename) {
FILE* fp;
struct Image img;
fp = fopen(filename, "r"); //Statement 1
if (fp == NULL)
{
printf("\nCan't open file or file doesn't exist.\r\n");
exit(0);
}
while (fread(&img, sizeof(img), 1, fp) > 0)
{
//if(strcmp(img.header,"IMG")==0)
//{
printf("\n\tHeader\twidth\theight\tdata\t\r\n");
printf("\n\t%s\t%d\t%d\t%s\r\n", img.header, img.width, img.height, img.data);
//integer overflow 0x7FFFFFFF+1=0
//0x7FFFFFFF+2 = 1
//will cause very large/small memory allocation.
int size1 = img.width + img.height;
char* buff1 = (char*)malloc(size1);
//heap buffer overflow
memcpy(buff1, img.data, sizeof(img.data));
free(buff1);
//double free
if (size1 / 2 == 0) {
free(buff1);
}
else {
//use after free
if (size1 / 3 == 0) {
buff1[0] = 'a';
}
}
//integer underflow 0-1=-1
//negative so will cause very large memory allocation
int size2 = img.width - img.height + 100;
//printf("Size1:%d",size1);
char* buff2 = (char*)malloc(size2);
//heap buffer overflow
memcpy(buff2, img.data, sizeof(img.data));
//divide by zero
int size3 = img.width / img.height;
//printf("Size2:%d",size3);
char buff3[10];
char* buff4 = (char*)malloc(size3);
memcpy(buff4, img.data, sizeof(img.data));
//OOBR read bytes past stack/heap buffer
char OOBR = buff3[size3];
char OOBR_heap = buff4[size3];
//OOBW write bytes past stack/heap buffer
buff3[size3] = 'c';
buff4[size3] = 'c';
if (size3 > 10) {
//memory leak here
buff4 = 0;
}
else {
free(buff4);
}
int size4 = img.width * img.height;
if (size4 / 2 == 0) {
//stack exhaustion here
stack_operation();
}
else {
//heap exhaustion here
char* buff5;
do {
buff5 = (char*)malloc(size4);
} while (buff5);
}
free(buff2);
//}
//else
// printf("invalid header\r\n");
}
fclose(fp);
return 0;
}
int main(int argc, char** argv)
{
printf("[+] %s() offset: 0x%x\n", __FUNCTION__, (char*)(*&main) - (char*)GetModuleHandleA(NULL));
printf("[+] %s() offset: 0x%x\n", __FUNCTION__, (char*)(*&ProcessImage) - (char*)GetModuleHandleA(NULL));
ProcessImage(argv[1]);
return 0;
}
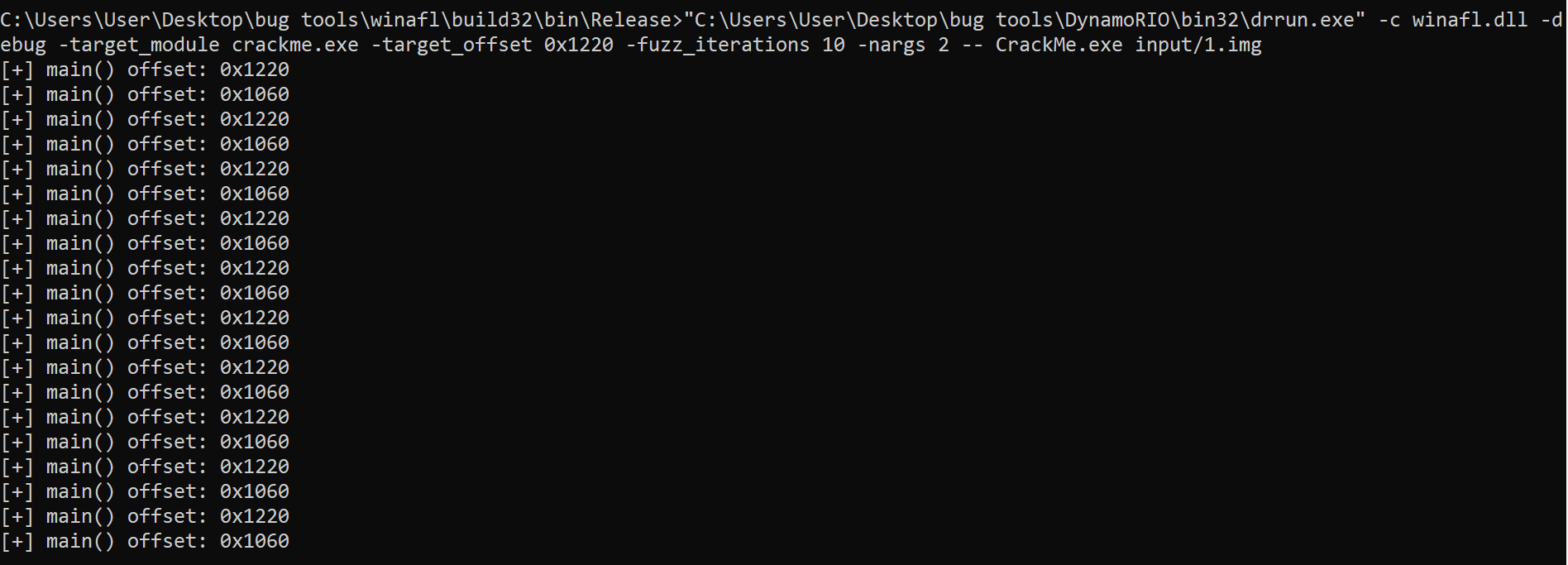
The main function is situated is at offset 0x1220 and ProcessImage is at 0x1060.
Here is the result of debug with offset 0x1220 (main function):
Module loaded, CrackMe.exe
Module loaded, aswhook.dll
Module loaded, VCRUNTIME140.dll
Module loaded, KERNEL32.dll
Module loaded, KERNELBASE.dll
Module loaded, ucrtbase.dll
Module loaded, ntdll.dll
Module loaded, dynamorio.dll
Module loaded, drmgr.dll
Module loaded, drwrap.dll
Module loaded, winafl.dll
Module loaded, drx.dll
Module loaded, drreg.dll
In pre_fuzz_handler
In post_fuzz_handler
In pre_fuzz_handler
In post_fuzz_handler
In pre_fuzz_handler
In post_fuzz_handler
In pre_fuzz_handler
In post_fuzz_handler
In pre_fuzz_handler
In post_fuzz_handler
In pre_fuzz_handler
In post_fuzz_handler
In pre_fuzz_handler
In post_fuzz_handler
In pre_fuzz_handler
In post_fuzz_handler
In pre_fuzz_handler
In post_fuzz_handler
In pre_fuzz_handler
In post_fuzz_handler
Everything appears to be running normally.
Coverage map follows:
The coverage map is full of null bytes, seems wrong?
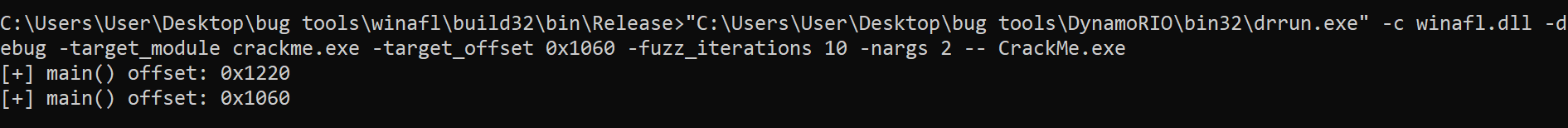
Here is the result of debug with offset 0x1060 (ProcessImage function):
Module loaded, CrackMe.exe
Module loaded, aswhook.dll
Module loaded, VCRUNTIME140.dll
Module loaded, KERNEL32.dll
Module loaded, KERNELBASE.dll
Module loaded, ucrtbase.dll
Module loaded, ntdll.dll
Module loaded, dynamorio.dll
Module loaded, drmgr.dll
Module loaded, drwrap.dll
Module loaded, winafl.dll
Module loaded, drx.dll
Module loaded, drreg.dll
In pre_fuzz_handler
About to make IsProcessorFeaturePresent(23) returns 0
Exception caught: c0000417
WARNING: Post-fuzz handler was never reached. Did the target function return normally?
Coverage map follows:
The coverage map again contains only null bytes.
Running afl-fuzz against both offsets returns the following:
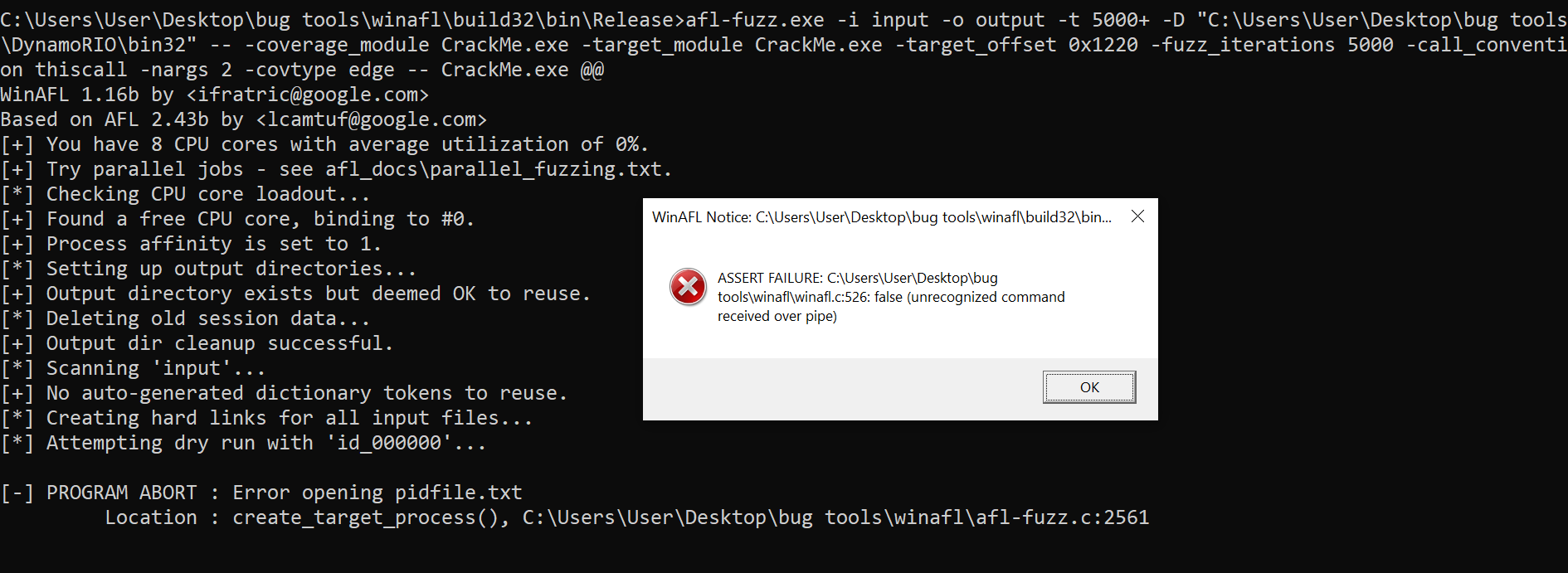
Here is the used command:
afl-fuzz.exe -i input -o output -t 5000+ -D "C:\Users\User\Desktop\bug tools\DynamoRIO\bin32" -- -coverage_module CrackMe.exe -target_module CrackMe.exe -target_offset 0x1060 -fuzz_iterations 5000 -call_convention thiscall -nargs 2 -covtype edge -- CrackMe.exe @@
Any ideas? Thank you
The coverage map containing null bytes is normal, that's because you haven't passed any -coverage_module at that point. The debug log for offset 0x1220 looks correct, but not for the other one.
Some questions that might help
- Which Windows version and which DynamoRIO version are you using? Did you build the latest WinAFL yourself?
- When running debug mode for offset 0x1060, have you tried changing
-call_convention?
Adding also @hardik05 who I see is author of your test target and might have some ideas.
Thank you for your reply @ifratric, completely removing the call convention argument did it!
It's a bit weird because I was following a Youtube tutorial, and the source code I used is provided by the creator, so the argument worked fine for him but not me, but hey, I can't complain, just glad I have it running.
Thank you again!