miasm
 miasm copied to clipboard
miasm copied to clipboard
Reverse engineering framework in Python
Function [_dis_block](https://github.com/cea-sec/miasm/blob/2a1a689a17a75232d598216b4d9265be7bd479f3/miasm/core/asmblock.py#L1430) could try to recognize jump tables
- Support Windows ApiSet - Refactor Sandbox - Refactor Loader :warning: The Sandbox `__init__` API has changed. Examples provided in `example/jitter` show new calling arguments
In my extension of `LifterModelCall_x86_32` i would like to model `float_st0` returns or arguments in the `call_effects` function. This is currently not possible because neither `ExprOp` nor `ExprAssign` allows mixed...
Hi, For my project i would like to modify the assembly graph to make the analysis easier. At the moment i added 2 modifications: - convert jump tables to an...
Issue created following #1328 To be sound, we must delete memory aliases after call execution. For the moment, interferences are only computed between the propagated value and the *destinations* of...
Hello, what are your thoughts on making the `Sanbox`es available through `Machine`? I think that architecture dependent classes such as [Sandbox_Linux_x86_32](https://github.com/cea-sec/miasm/blob/master/miasm/analysis/sandbox.py#L577) could be moved to a separate file such as...
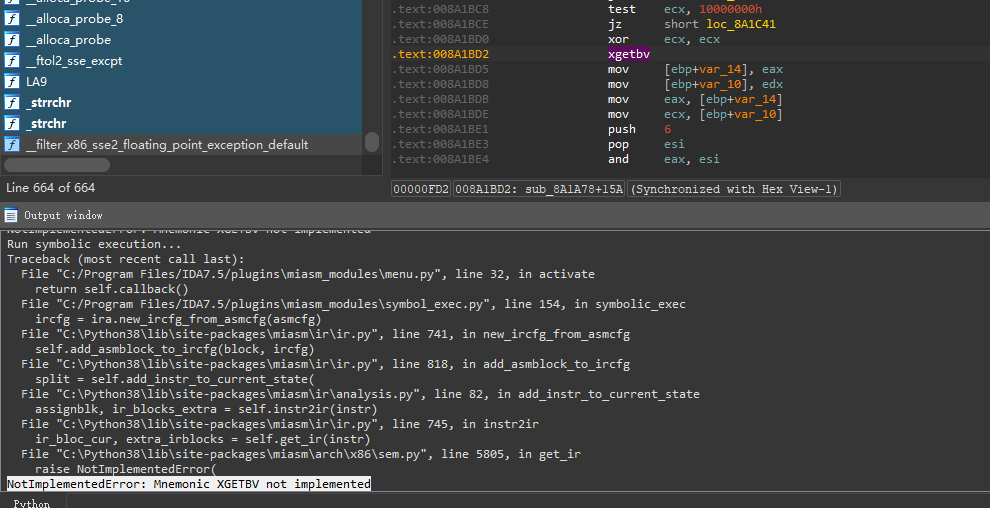 `.text:008A1BBB A3 10 F0 8B 00 mov dword_8BF010, eax .text:008A1BC0 F7 C1 00 00 00 08 test ecx, 8000000h .text:008A1BC6 74 79 jz short loc_8A1C41 .text:008A1BC8 F7 C1 00...
Add possibility to diff states in dump func of symbexec
Hello Team, Here is a patch that fixes the build on MacOS 10.14. When checkouting the code and building, I came accross this error: ```sh /usr/bin/clang -fno-strict-aliasing -fno-common -dynamic -pipe...
Hello, I want to use miasm to symboliclly execute a single function in ELF, with the sub functions called inside skipped but with args logged. I modied code from dse_crackme.py...
