Access an arn of a AWS::IAM::Role resource created using cloudformation in a later code build deploy stage in the same pipeline
I am trying to access a S3 bucket in another AWS account by assuming role through a deploy code build step and for that I need to get the ARN of the AWS::IAM::Role resource but since the AWS::IAM::Role resource is in the same account of s3 bucket and I am running the pipeline in a different account I am struggling to do it because I didn't find any way to get the ARN of AWS::IAM::Role inside the codebuild deploy step. is there any way to achieve this without hardcoding the ARN of AWS::IAM::Role inside the codebuild buildspec file.
Hey @csmuthukuda Would this help you? https://github.com/awslabs/aws-deployment-framework/blob/8ae0f35da64e90da3790935a664908e3e5adf133/docs/user-guide.md#importing-output-values
Thanks @StewartW do you have a sample code that I can look in to like this because I'm a little confused here since I think to do this I need to rebuild the parameters to include it in the params and after that maybe I can access them..Is that correct?
Would you be able to share a sanitised gist of your deployment map and I could take a look?
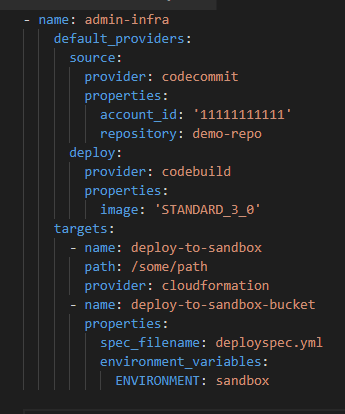
@StewartW here you can see that I am building my infrastructure using cloudformation first and then I am using an additional codebuild step to deploy the build to s3 bucket. what I need to achieve is take the Iam Role created from the cloudformation step, inside the later codebuild step.
@csmuthukuda You could also use a mono-repo or multi-pipeline setup, to get the role configured and use it in another pipeline.
So the first pipeline is responsible for the IAM role to be created. The other pipeline is importing it through the params folder as explained by @StewartW.
I'm closing this issue as it has been inactive for a long period of time. This probably means that it is not reproducible or it has been fixed in the meanwhile.
Please reopen if you still encounter this issue with the latest stable version.
Thank you!