NewNtdllBypassInlineHook_CSharp
 NewNtdllBypassInlineHook_CSharp copied to clipboard
NewNtdllBypassInlineHook_CSharp copied to clipboard
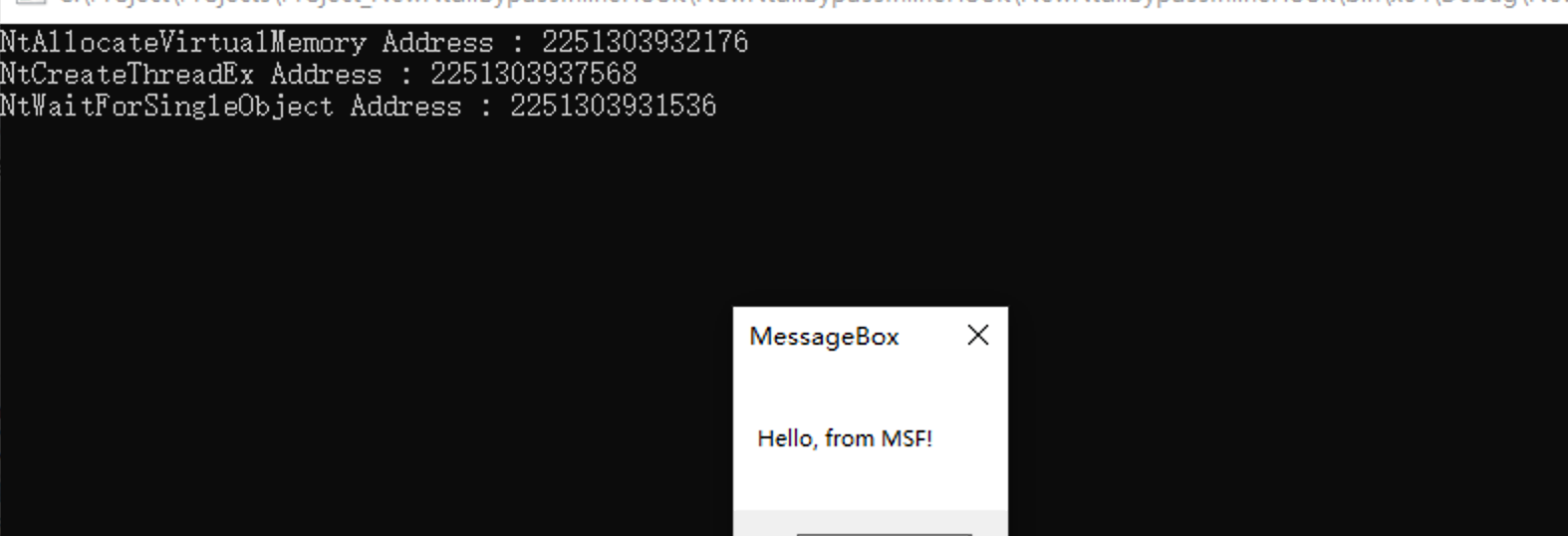
Load a fresh new copy of ntdll.dll via file mapping to bypass API inline hook.
NewNtdllBypassInlineHook
Blog link: working on it
-
Base on my other projects down below.
-
Use a clean version of ntdll.dll, and import function from this ntdll.dll.
-
Only testd on Win10/x64, may need some modifications on <MainFunction.cs> to works on x86.
-
Steps
- Load a fresh new copy of ntdll.dll via file mapping.
- Load the copy into memroy and get a "BaseAddress".
- Use the "BaseAddress" and function's name, function's RVA to find function's address.
- Export the function's address and use the function via "delegate".
- Shellcode execute.
-
You could even modify the code to:
- Classic process injection.
- MappingInjection(https://github.com/Kara-4search/MappingInjection_CSharp)
- APCexecution(https://github.com/Kara-4search/APC_ShellcodeExecution_CSharp)
- EarlyBirdInjection(https://github.com/Kara-4search/EarlyBirdInjection_CSharp)
-
The shellcode below is a messagebox
/* MessageBox */
byte[] buf1 = new byte[323] {
0xfc,0x48,0x81,0xe4,0xf0,0xff,0xff,0xff,0xe8,0xd0,0x00,0x00,0x00,0x41,0x51,
0x41,0x50,0x52,0x51,0x56,0x48,0x31,0xd2,0x65,0x48,0x8b,0x52,0x60,0x3e,0x48,
0x8b,0x52,0x18,0x3e,0x48,0x8b,0x52,0x20,0x3e,0x48,0x8b,0x72,0x50,0x3e,0x48,
0x0f,0xb7,0x4a,0x4a,0x4d,0x31,0xc9,0x48,0x31,0xc0,0xac,0x3c,0x61,0x7c,0x02,
0x2c,0x20,0x41,0xc1,0xc9,0x0d,0x41,0x01,0xc1,0xe2,0xed,0x52,0x41,0x51,0x3e,
0x48,0x8b,0x52,0x20,0x3e,0x8b,0x42,0x3c,0x48,0x01,0xd0,0x3e,0x8b,0x80,0x88,
0x00,0x00,0x00,0x48,0x85,0xc0,0x74,0x6f,0x48,0x01,0xd0,0x50,0x3e,0x8b,0x48,
0x18,0x3e,0x44,0x8b,0x40,0x20,0x49,0x01,0xd0,0xe3,0x5c,0x48,0xff,0xc9,0x3e,
0x41,0x8b,0x34,0x88,0x48,0x01,0xd6,0x4d,0x31,0xc9,0x48,0x31,0xc0,0xac,0x41,
0xc1,0xc9,0x0d,0x41,0x01,0xc1,0x38,0xe0,0x75,0xf1,0x3e,0x4c,0x03,0x4c,0x24,
0x08,0x45,0x39,0xd1,0x75,0xd6,0x58,0x3e,0x44,0x8b,0x40,0x24,0x49,0x01,0xd0,
0x66,0x3e,0x41,0x8b,0x0c,0x48,0x3e,0x44,0x8b,0x40,0x1c,0x49,0x01,0xd0,0x3e,
0x41,0x8b,0x04,0x88,0x48,0x01,0xd0,0x41,0x58,0x41,0x58,0x5e,0x59,0x5a,0x41,
0x58,0x41,0x59,0x41,0x5a,0x48,0x83,0xec,0x20,0x41,0x52,0xff,0xe0,0x58,0x41,
0x59,0x5a,0x3e,0x48,0x8b,0x12,0xe9,0x49,0xff,0xff,0xff,0x5d,0x49,0xc7,0xc1,
0x00,0x00,0x00,0x00,0x3e,0x48,0x8d,0x95,0x1a,0x01,0x00,0x00,0x3e,0x4c,0x8d,
0x85,0x2b,0x01,0x00,0x00,0x48,0x31,0xc9,0x41,0xba,0x45,0x83,0x56,0x07,0xff,
0xd5,0xbb,0xe0,0x1d,0x2a,0x0a,0x41,0xba,0xa6,0x95,0xbd,0x9d,0xff,0xd5,0x48,
0x83,0xc4,0x28,0x3c,0x06,0x7c,0x0a,0x80,0xfb,0xe0,0x75,0x05,0xbb,0x47,0x13,
0x72,0x6f,0x6a,0x00,0x59,0x41,0x89,0xda,0xff,0xd5,0x48,0x65,0x6c,0x6c,0x6f,
0x2c,0x20,0x66,0x72,0x6f,0x6d,0x20,0x4d,0x53,0x46,0x21,0x00,0x4d,0x65,0x73,
0x73,0x61,0x67,0x65,0x42,0x6f,0x78,0x00 };
Usage
- Just launch through a white-list application
TO-DO list
- Works on both x64/x86
Update history
- Restructure Code - 20210903
- Remove unnecessary code in NativeFunctions.cs - 20210906
Reference link:
1. https://docs.microsoft.com/en-us/windows/win32/api/fileapi/nf-fileapi-createfilea
2. http://pinvoke.net/default.aspx/kernel32/CreateFile.html
3. https://idiotc4t.com/defense-evasion/load-ntdll-too
4. http://blog.leanote.com/post/snowming/a0366d1d01bf
5. https://docs.microsoft.com/en-us/windows-hardware/drivers/ddi/ntifs/nf-ntifs-ntallocatevirtualmemory
6. https://docs.microsoft.com/en-us/windows/win32/api/processthreadsapi/nf-processthreadsapi-createthread
7. http://pinvoke.net/default.aspx/ntdll/NtCreateThreadEx.html
8. https://blog.sektor7.net/#!res/2021/halosgate.md
9. https://www.ired.team/offensive-security/defense-evasion/using-syscalls-directly-from-visual-studio-to-bypass-avs-edrs
10. https://docs.microsoft.com/en-us/windows/win32/api/processthreadsapi/nf-processthreadsapi-createremotethread
11. http://pinvoke.net/default.aspx/kernel32/CreateFile.html
12. https://idiotc4t.com/defense-evasion/load-ntdll-too
13. https://makosecblog.com/malware-dev/dll-unhooking-csharp/