Validation does not evaluate the entire chain
Describe the bug
The check will not show WARNING or CRITICAL if the server is presenting a full chain with 'remaining time of ca/intermediate less than leaf certificate'.
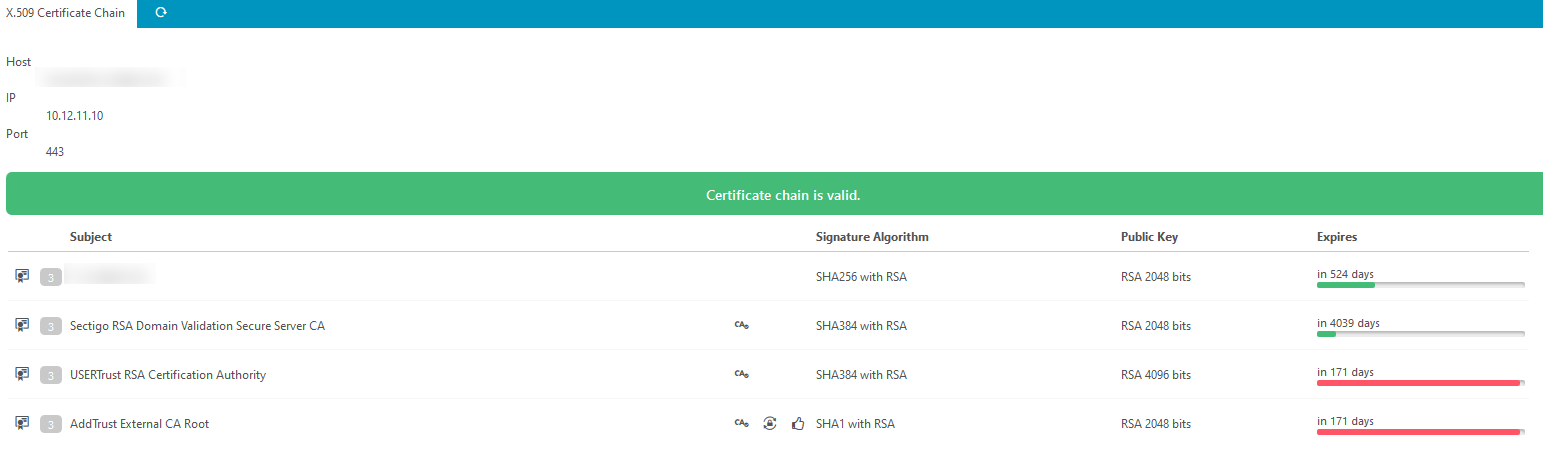
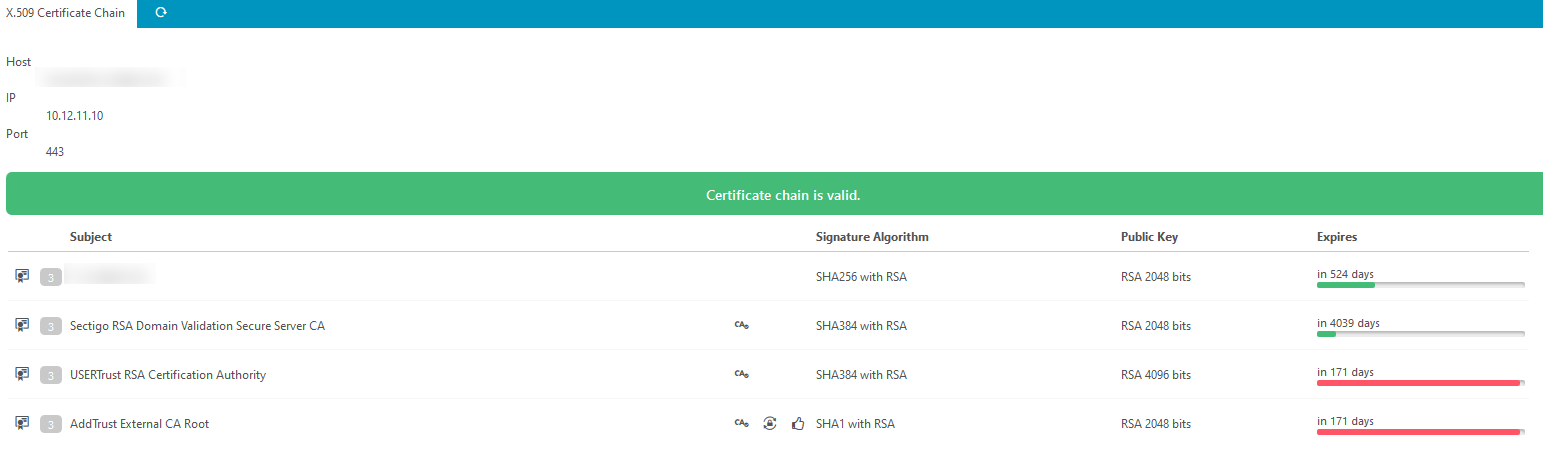
the following example is showing an example of the certificate usage in that case and reports 'OK - .... expires in 524 days'
To Reproduce
import some certificate chain with specific data. essential example data is given below in the table in section 'Additional context'.
background: cross signing certificates often used to transform CAs. In such situations it might happen that more than one certificate path is possible. For details see the current case with sectigo certificates: https://support.sectigo.com/Com_KnowledgeDetailPageFaq?Id=kA01N000000rgSZ
Expected behavior
CheckCommand should evaluate the whole chain.
Screenshots
this is shown in the description above:
Your Environment
This is an implementation bug it will happen in any version i checked.
- Icinga Web 2 version and modules (System - About):
- Web browser used:
- Icinga 2 version used (
icinga2 --version): - PHP version used (
php --version): - Server operating system and version:
Additional context
I modified the query from the check slightly to show case more insights of this problem.
SELECT c.id,
t.port,
cc.valid,
cc.invalid_reason,
c.subject,
ci.self_signed as ci_ss,
c.self_signed as c_ss,
COALESCE(ci.self_signed, c.self_signed) as self_signed,
c.valid_from,
c.valid_to,
ccl.`order`
FROM x509_target t
JOIN x509_certificate_chain cc ON cc.id = t.latest_certificate_chain_id
JOIN x509_certificate_chain_link ccl ON ccl.certificate_chain_id = cc.id
JOIN x509_certificate c ON c.id = ccl.certificate_id
LEFT JOIN x509_certificate ci ON ci.subject_hash = c.issuer_hash
WHERE t.hostname = 'hallo.mywildcard.com' and
t.port = 443
ORDER BY ccl.`order` ASC;
| id | port | valid | invalid_reason | subject | ci_ss | c_ss | self_signed | valid_from | valid_to | order |
|---|---|---|---|---|---|---|---|---|---|---|
| 40 | 443 | yes | NULL | *.mywildcard.com | no | no | no | 1558137600 | 1621295999 | 0 |
| 10 | 443 | yes | NULL | Sectigo RSA Domain Validation Secure Server CA | no | no | no | 1541116800 | 1924991999 | 1 |
| 10 | 443 | yes | NULL | Sectigo RSA Domain Validation Secure Server CA | yes | no | yes | 1541116800 | 1924991999 | 1 |
| 41 | 443 | yes | NULL | USERTrust RSA Certification Authority | yes | no | yes | 959683718 | 1590835718 | 2 |
| 36 | 443 | yes | NULL | AddTrust External CA Root | yes | yes | yes | 959683718 | 1590835718 | 3 |
that shows some more droubles here with the join and maybe the 2 cert chain pathes
see https://support.sectigo.com/Com_KnowledgeDetailPageFaq?Id=kA01N000000rgSZ