Reread TLS certificates in the backround
Prerequisites
Please answer the following questions for yourself before submitting an issue. YOU MAY DELETE THE PREREQUISITES SECTION.
- [X] I am running the latest version
- [X] I checked the documentation and found no answer
- [X] I checked to make sure that this issue has not already been filed
Issue Details
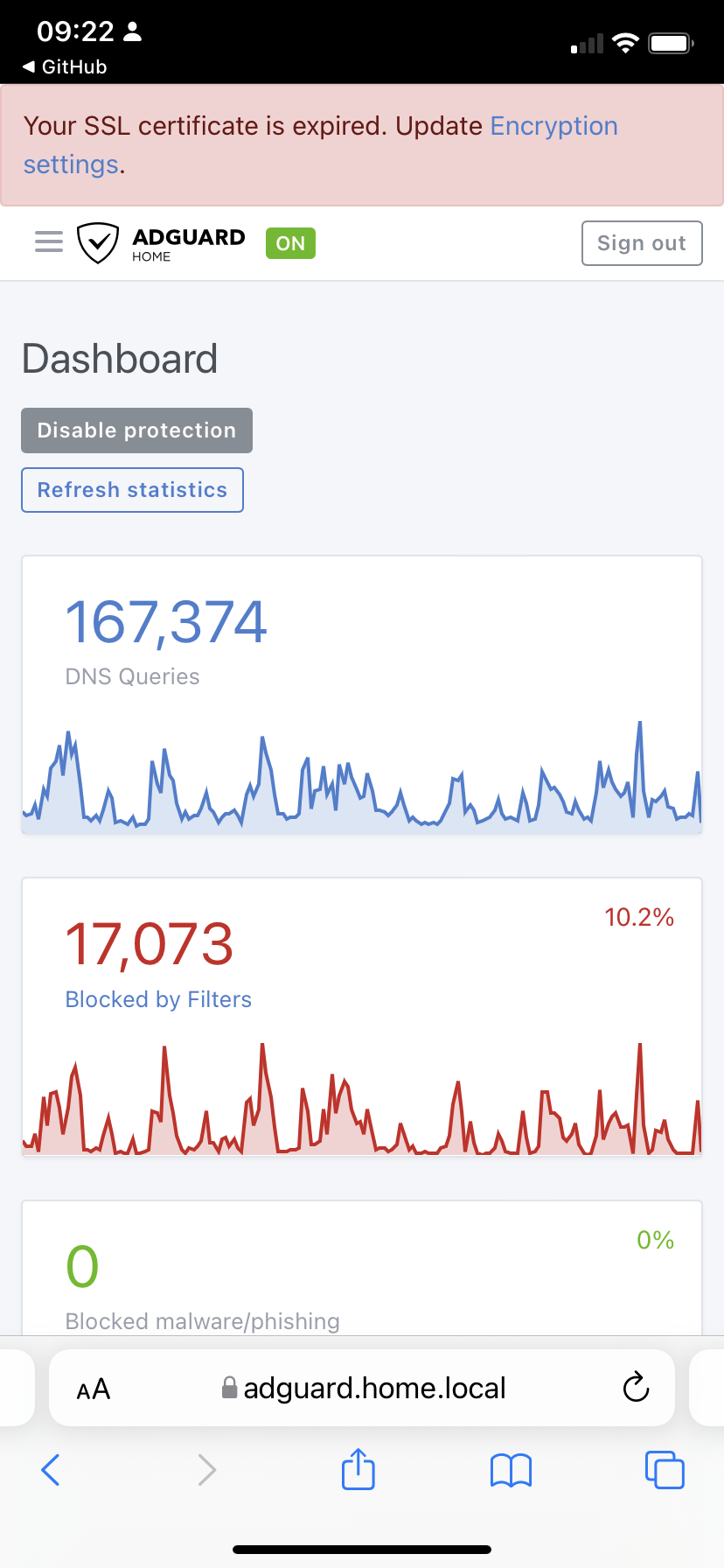
I am using Caddyserver to renew automatically my TLS certificates. It seems they are renewed every 12 hours which very small overlapping in validity (I don't know if it is possible to change that). After 12 hours when I try to login the AGH front end, Safari warns me that the certificate has expired and that the connection is not safe. If I open the site anyway, the first page tells me that certificate has expired (see attached). The renewed certificate is only taken into account when I go to the encryption setting page (where I have the path to the certificate and key).
-
Version of AdGuard Home server:
- v0.106.3
-
How did you install AdGuard Home:
- Docker
-
How did you setup DNS configuration:
- IoT
-
If it's a router or IoT, please write device model:
- NAS
Expected Behavior
Renewed TLS certificate to be taken into account in the background.
Actual Behavior
Renewed TLS certificate seems to be only taken into account when opening the encryption settings page.
Screenshots
Screenshot:
 <!— drag and drop, upload or paste your screenshot to this area—>
<!— drag and drop, upload or paste your screenshot to this area—>
Additional Information
The TLS certs are currently only updated when you either resave the encryption settings from the UI, or when you send SIGHUP to AGH.
@ameshkov, do we want some kind of background schedule to reload TLS certs in the future design / refactoring?
@ainar-g yeah, it makes sense to me.
I know that this is a slightly off-topic question, but if I am using Adguard-Home via Snap, where is the ideal place to store the let's encrypt certificates so that the snap container has access?
@nuka-cola
Somewhere inside this directory:
/var/snap/adguard-home/current
For AGH running in a snap this would be the cwd directory.
I.e. you can specify the path to the certificate as ./cert.crt
This is become more important when Let's Encrypt's 6 day certificate become available.
https://letsencrypt.org/2025/01/16/6-day-and-ip-certs/
Let's Encrypt will ship IP certificates and 6 days of certificate latter this year.
https://letsencrypt.org/2025/07/01/issuing-our-first-ip-address-certificate/
Let's Encrypt will ship IP certificates and 6 days of certificate soon, this is mandatory.