pwncat
 pwncat copied to clipboard
pwncat copied to clipboard
Unable to Find PowerSploit Source
Bug Description
@mgeddert reported this issue within another issue and via E-mail directly to me.
Roughly speaking, the attacker is attempting to load the PowerSploit Recon powershell modules in order to facilitate enumeration (specifically, user/group enumeration while running sessions). For some reason, pwncat can't find the Recon source, and raises an exception. This does not kill pwncat, and is caught by the interpreter. The following is the traceback I received via E-mail:
──╼ $pwncat -m windows -lp 9090
[11:57:05] Welcome to pwncat !
[11:57:41] received connection from 10.7.113.40:25915
[11:57:41] 0.0.0.0:9090: dropping stage one in '\\Windows\\Tasks\\gn0RkfdV'
[11:57:42] 0.0.0.0:9090: using install utils from .net v4.0.30319
10.7.113.40:25915: registered new host w/ db
(local) pwncat$
(local) pwncat$
(local) pwncat$
(local) pwncat$ sessions
[11:58:00] 10.7.113.40:25915: windows.enumerate.domain: usr/local/master/lib/python3.9/dist-packages/pwncat/data/PowerSploit/Recon/Get-ComputerDetail.ps1: psmodule not found
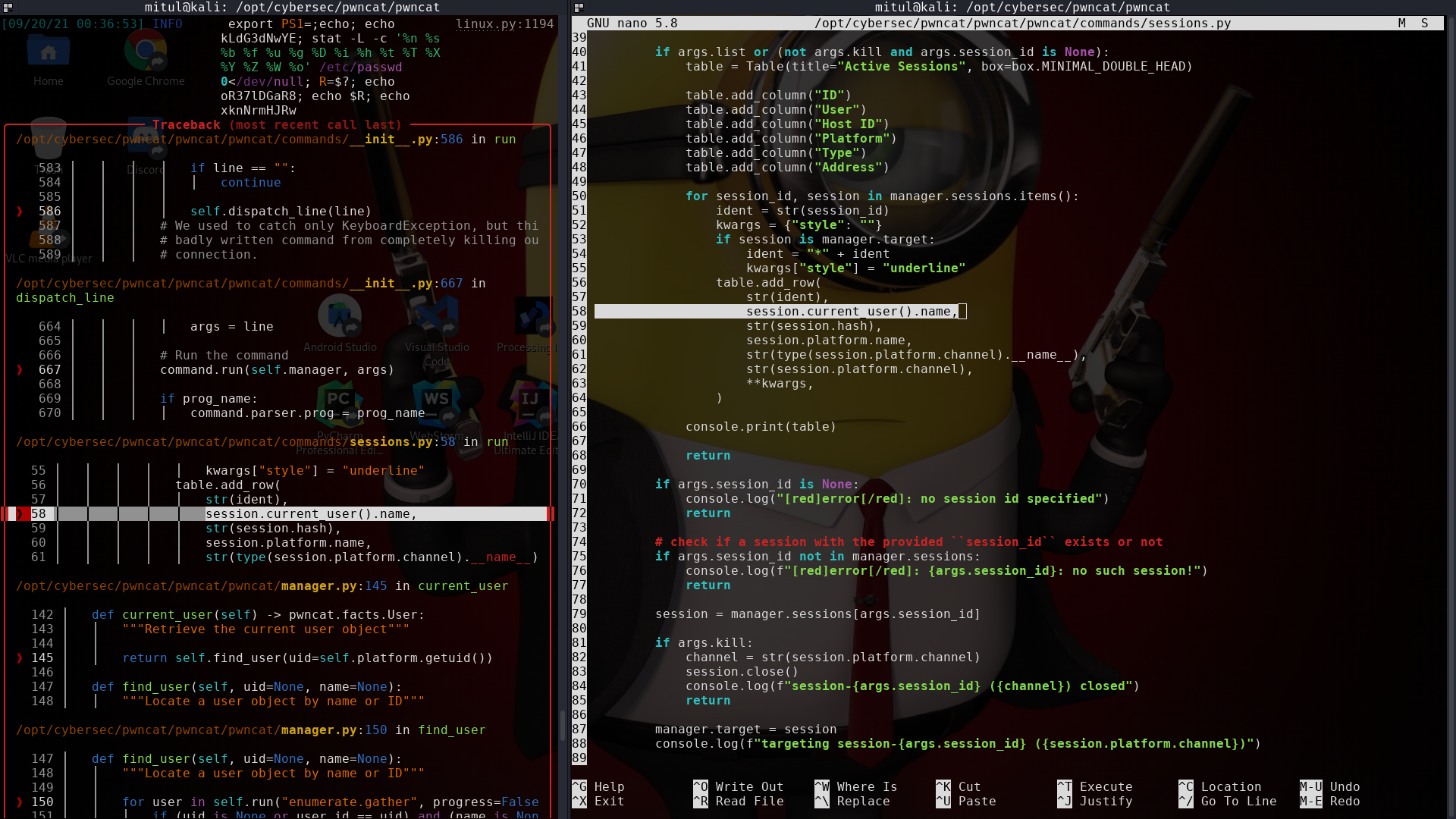
╭─────────────── Traceback (most recent call last) ─────────────────────────
│ /usr/local/lib/python3.9/dist-packages/pwncat/commands/__init__.py:586 in run
│
│ 583 │ │ │ │ if line == "":
│ 584 │ │ │ │ │ continue
│ 585 │ │ │ │
│ ❱ 586 │ │ │ │ self.dispatch_line(line)
│ 587 │ │ │ # We used to catch only KeyboardException, but this prevents a
│ 588 │ │ │ # badly written command from completely killing our remote
│ 589 │ │ │ # connection.
│
│ /usr/local/lib/python3.9/dist-packages/pwncat/commands/__init__.py:667 in dispatch_line
│
│ 664 │ │ │ │ args = line
│ 665 │ │ │
│ 666 │ │ │ # Run the command
│ ❱ 667 │ │ │ command.run(self.manager, args)
│ 668 │ │ │
│ 669 │ │ │ if prog_name:
│ 670 │ │ │ │ command.parser.prog = prog_name
│
│ /usr/local/lib/python3.9/dist-packages/pwncat/commands/sessions.py:58 in run
│
│ 55 │ │ │ │ │ kwargs["style"] = "underline"
│ 56 │ │ │ │ table.add_row(
│ 57 │ │ │ │ │ str(ident),
│ ❱ 58 │ │ │ │ │ session.current_user().name,
│ 59 │ │ │ │ │ str(session.hash),
│ 60 │ │ │ │ │ session.platform.name,
│ 61 │ │ │ │ │ str(type(session.platform.channel).__name__),
╰─────────────────────────────────────────────────────
AttributeError: 'NoneType' object has no attribute 'name'
(local) pwncat$
pwncat version
Based on the previous Parrot OS issue, I'm assuming you are on 0.4.3, but please correct me if I am wrong.
$ pwncat --version
0.4.3
Target System (aka "victim")
The only thing I know is that the target is a Windows host.
This was originally reported within #201.
Looks like it is time to revive my Windows VMs :laughing:
Using commit 921264caab52250f027356bc208ec19369c2acbf
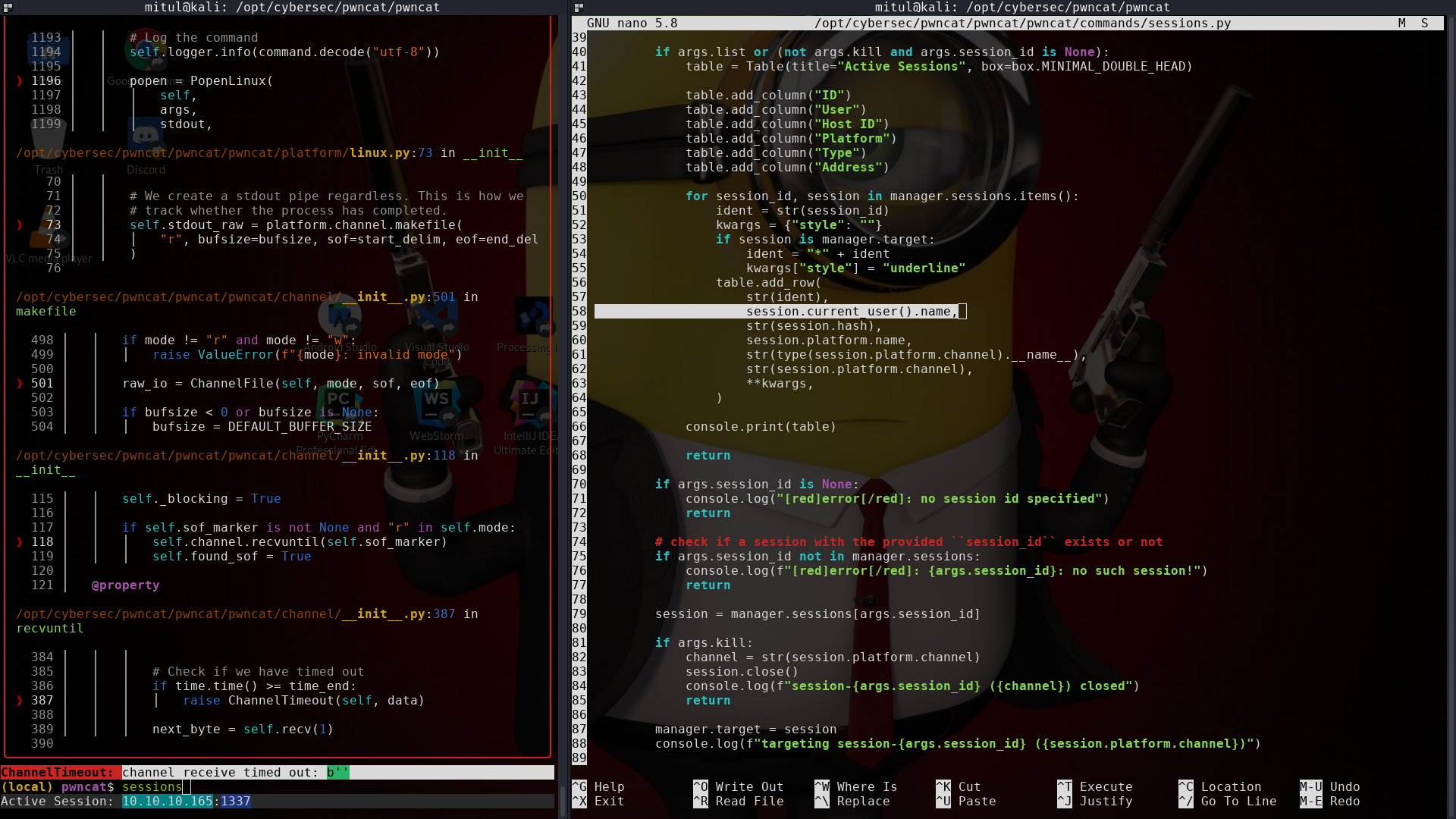
While running some modules, preferably run enumerate, self.dispatch_line(line) seems to be causing some issue
Because either the Platform.command_running (!= None) or line is not cleared while the current command has failed
For example, our last action executed ...; dd if=/etc/passwd 0</dev/null; ... and it didn't finish properly leaving the traces into line variable which are re-executed on the very next action causing some wierd issues
Here, I found a similar error with a Linux target
Running sessions doesn't go well
I once received channel receive timed out: b'traces of last command ran by pwncat'
I will update this once I figure out the exact issue